Discover the IT Security add-on
Your virtual SOC analyst for AI-powered behavioral threat detection
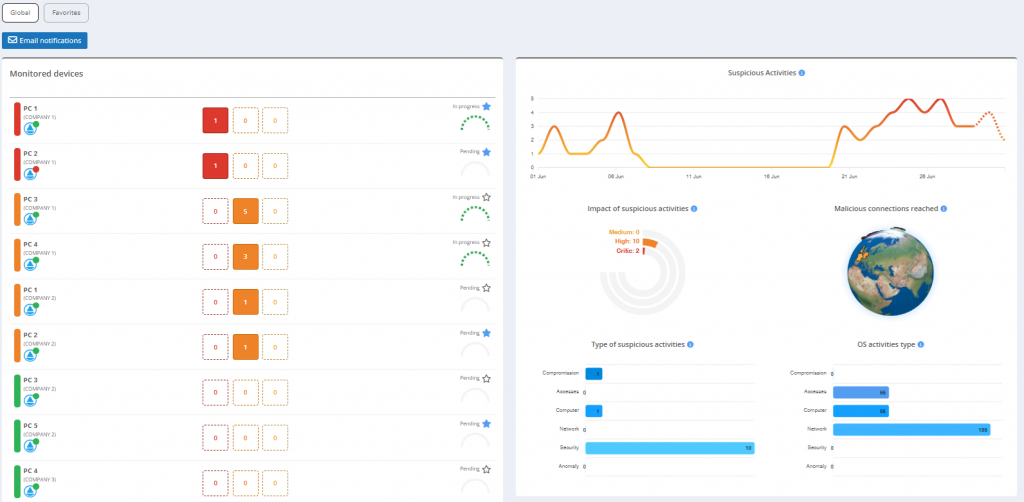
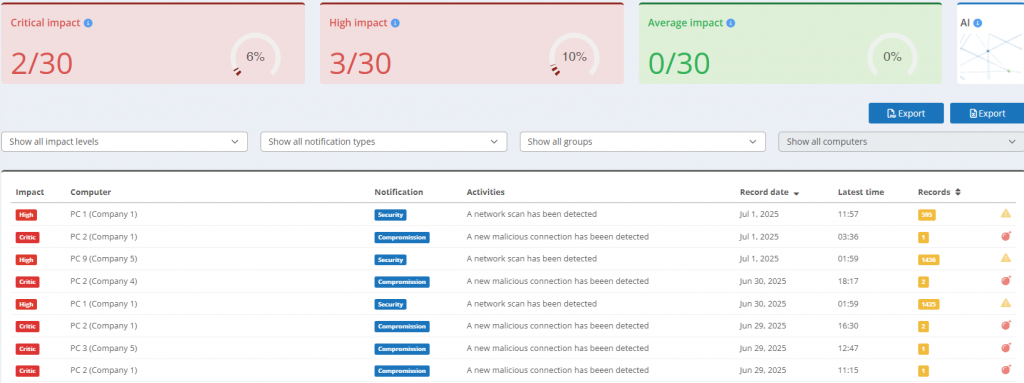
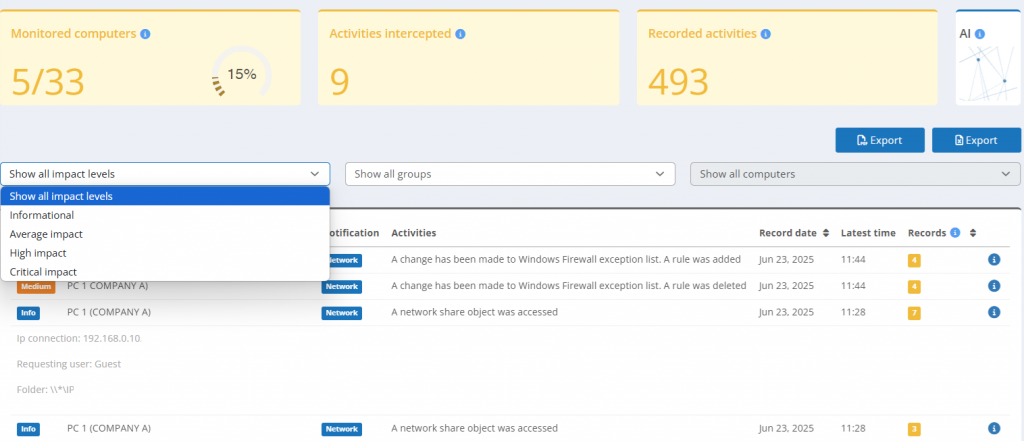
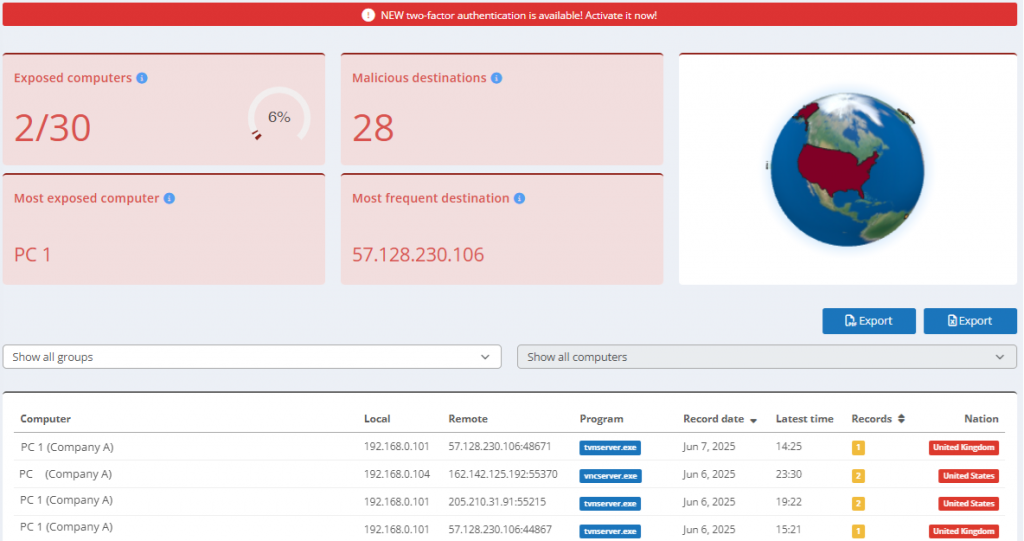
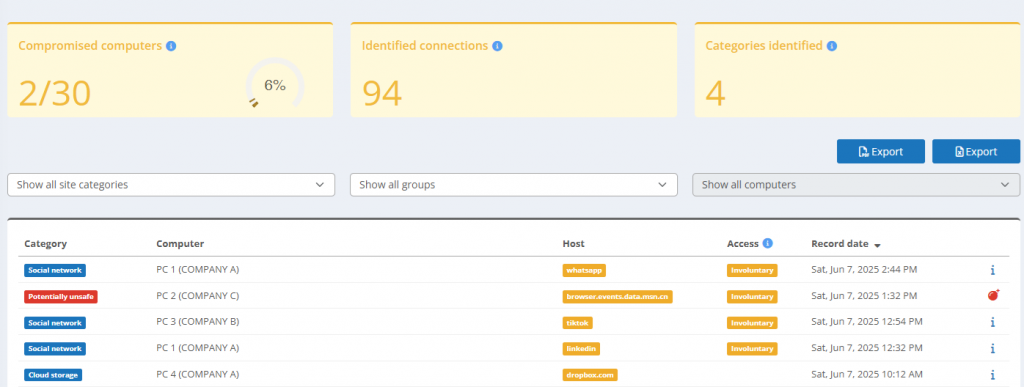
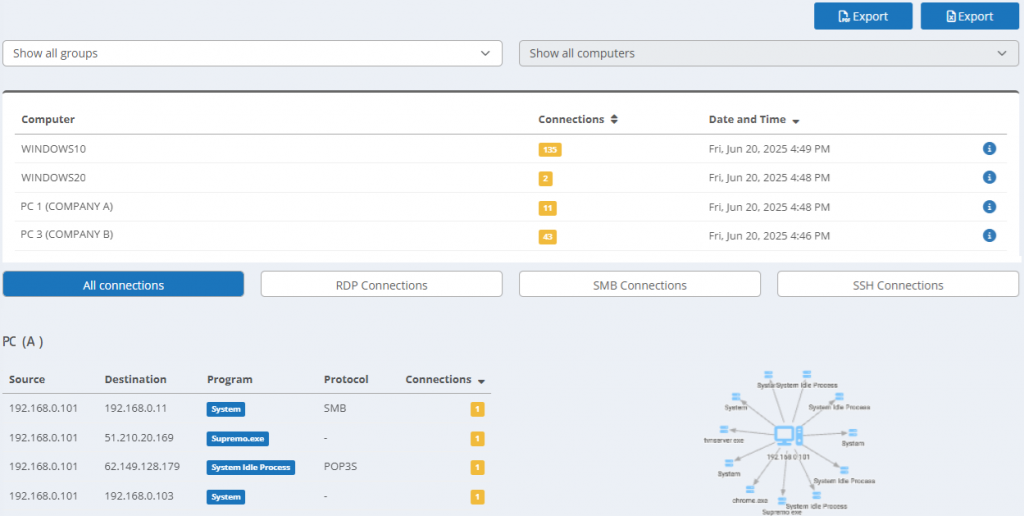
The IT Security add-on is an endpoint protection add-on for Supremo Console, designed to detect threats that traditional antivirus can miss. By leveraging self-learning AI, it identifies suspicious behaviors across users, devices, and networks, enabling precise threat detection.
Key Features
Tailored for IT teams, MSPs and SMBs, this AI-powered cybersecurity solution (powered by LECS®) combines real-time monitoring, anomaly analysis, and rapid incident response, all from a single integrated dashboard.
Simplify threat detection and enhance monitoring capabilities with AI-powered intelligence
Why choose the IT Security add-on
Acting as a virtual SOC, this add-on continuously adapts to IT environments. It empowers you to secure endpoints, without complex setup or prohibitive costs.
Experience the Supremo IT Security
Protect your business with smart, scalable cybersecurity designed for real-world challenges.

 Français
Français
 Deutsch
Deutsch
 Italiano
Italiano
 Português
Português
 Español
Español